How to Deploy SFTPGo as an AWS Transfer Family Alternative
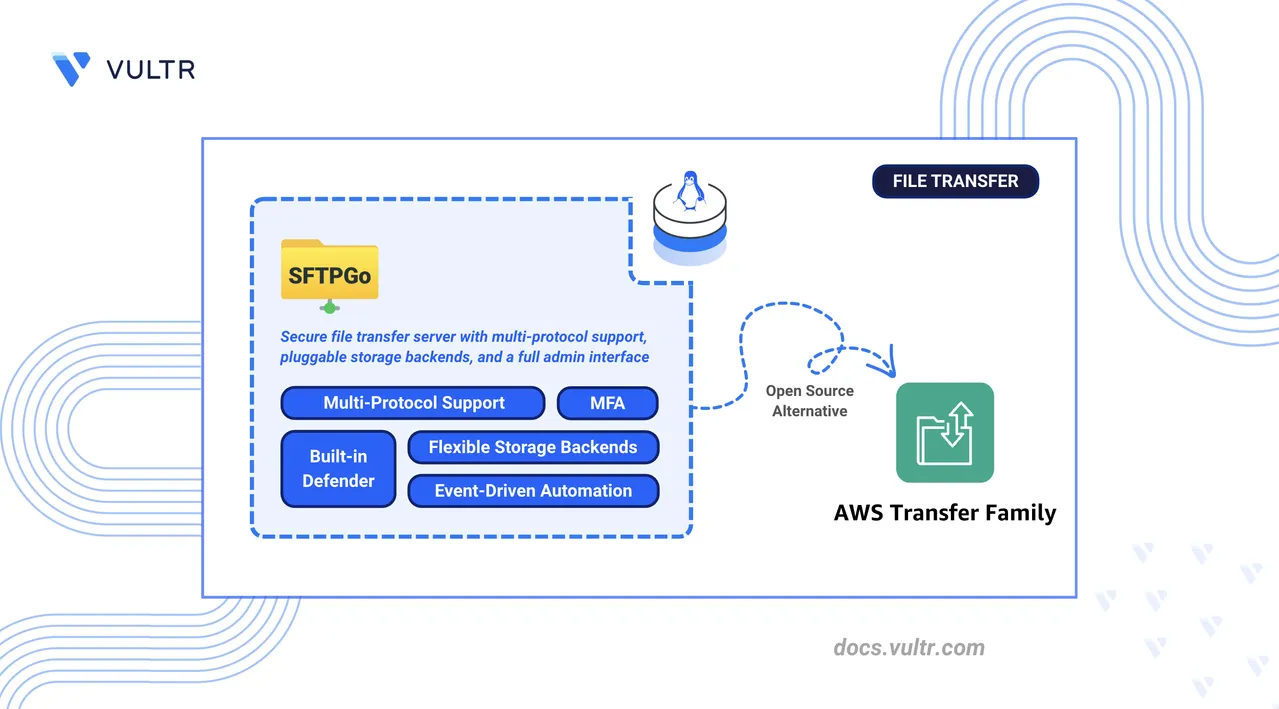
AWS Transfer Family is Amazon's managed file transfer service that provides SFTP, FTP/S, and FTPS endpoints with S3 and EFS storage backends as hosted services within the AWS ecosystem. It abstracts server management but ties teams to AWS-specific IAM authentication, per-protocol endpoint pricing, and hourly charges regardless of usage.
SFTPGo is an open-source file transfer server that replaces Transfer Family with a self-hosted deployment supporting SFTP, FTP/S, and WebDAV. It provides equivalent user management, S3-compatible storage backends, and multi-protocol access on any infrastructure without per-endpoint billing or AWS API dependencies.
This article explains how to deploy SFTPGo as a self-hosted alternative to AWS Transfer Family using Docker Compose with Traefik for automatic HTTPS. It covers user authentication with SSH keys and passwords, storage backend configuration with local filesystem and S3-compatible object storage, multi-protocol access (SFTP, FTP/S, WebDAV), event notifications, and migration from AWS Transfer Family.
Understanding SFTPGo Architecture
The following table maps AWS Transfer Family components to their SFTPGo equivalents:
| AWS Transfer Family | SFTPGo Equivalent | Description |
|---|---|---|
| SFTP Endpoint | SFTPGo SFTP Server | Accepts SFTP connections on a configurable port (default: 2022). |
| Transfer Family Users | SFTPGo User Management | Create and manage users via the web interface or REST API. |
| S3 Storage Integration | S3-Compatible Backend | Connect to any S3-compatible storage service. |
| AWS Management Console | Web Admin Interface | Browser-based dashboard for configuration and monitoring. |
| IAM/Identity Providers | Authentication Methods | SSH keys, passwords, LDAP, and external HTTP authentication. |
| Custom Hostname | Custom Domain | Configure a custom domain with TLS certificates. |
| CloudWatch Logs | Event Logging | Built-in logging with webhook and external integrations. |
| Per-user Bandwidth | Bandwidth Throttling | Configure upload and download limits per user. |
SFTPGo runs as a single binary or Docker container that handles all protocols and administrative functions. The architecture includes:
- Protocol Handlers: Separate listeners for SFTP (port
2022), FTP/S (port2121), and WebDAV (port10080). - Web Admin Interface: Management dashboard accessible on port
8080. - Data Provider: SQLite (default), MySQL, or PostgreSQL database for user and configuration storage.
- Storage Backends: Local filesystem, S3-compatible storage (including Vultr Object Storage), Azure Blob, or Google Cloud Storage.
Prerequisites
Before you begin, you need to:
- Have access to a Linux-based server as a non-root user with sudo privileges.
- Install Docker and Docker Compose.
- Create a DNS A record pointing to your server's IP address (for example,
sftp.example.com). - (Optional) Provision an S3-compatible object storage bucket for cloud storage backends.
Deploy SFTPGo with Docker Compose
Docker Compose orchestrates the SFTPGo and Traefik containers, defines persistent storage volumes, and manages networking between services.
Create the project directory with subdirectories for data and configuration persistence.
console$ mkdir -p ~/sftpgo/{data,config}
Navigate to the project directory.
console$ cd ~/sftpgo
Create the
.envfile to store the domain and Let's Encrypt email used by Traefik.console$ nano .env
Add the following variables. Replace
sftp.example.comwith your domain andadmin@example.comwith your email address.iniDOMAIN=sftp.example.com LETSENCRYPT_EMAIL=admin@example.com
Save and close the file.
Create the Docker Compose configuration file.
console$ nano docker-compose.yml
Add the following configuration:
yamlservices: traefik: image: traefik:v3.6 container_name: traefik command: - "--providers.docker=true" - "--providers.docker.exposedbydefault=false" - "--entrypoints.web.address=:80" - "--entrypoints.websecure.address=:443" - "--entrypoints.web.http.redirections.entrypoint.to=websecure" - "--certificatesresolvers.letsencrypt.acme.httpchallenge=true" - "--certificatesresolvers.letsencrypt.acme.httpchallenge.entrypoint=web" - "--certificatesresolvers.letsencrypt.acme.email=${LETSENCRYPT_EMAIL}" - "--certificatesresolvers.letsencrypt.acme.storage=/letsencrypt/acme.json" ports: - "80:80" - "443:443" volumes: - "./letsencrypt:/letsencrypt" - "/var/run/docker.sock:/var/run/docker.sock:ro" restart: unless-stopped sftpgo: image: drakkan/sftpgo:v2.6 container_name: sftpgo restart: unless-stopped ports: - "2022:2022" - "2121:2121" - "10080:10080" environment: - SFTPGO_HTTPD__BINDINGS__0__PORT=8080 - SFTPGO_HTTPD__BINDINGS__0__ADDRESS=0.0.0.0 - SFTPGO_SFTPD__BINDINGS__0__PORT=2022 - SFTPGO_FTPD__BINDINGS__0__PORT=2121 - SFTPGO_WEBDAVD__BINDINGS__0__PORT=10080 - SFTPGO_DATA_PROVIDER__DRIVER=sqlite - SFTPGO_DATA_PROVIDER__NAME=/var/lib/sftpgo/sftpgo.db volumes: - ./data:/srv/sftpgo - ./config:/var/lib/sftpgo labels: - "traefik.enable=true" - "traefik.http.routers.sftpgo.rule=Host(`${DOMAIN}`)" - "traefik.http.routers.sftpgo.entrypoints=websecure" - "traefik.http.routers.sftpgo.tls.certresolver=letsencrypt" - "traefik.http.services.sftpgo.loadbalancer.server.port=8080" healthcheck: test: ["CMD", "sftpgo", "ping", "-c", "/var/lib/sftpgo"] interval: 30s timeout: 10s retries: 3
Save and close the file.
The configuration exposes:
- Port 80, 443: Traefik HTTP/HTTPS entry points for the web admin interface.
- Port 2022: SFTP protocol connections.
- Port 2121: FTP/S protocol connections.
- Port 10080: WebDAV protocol connections.
Traefik routes the web admin interface (internal port
8080) through HTTPS on the configured domain using Let's Encrypt certificates.Start the SFTPGo and Traefik containers.
console$ docker compose up -d
Verify the container is running.
console$ docker compose ps
The output displays two running containers: SFTPGo and Traefik with Traefik listening on ports 80 and 443.
Check the service logs for any errors.
console$ docker compose logs
For more information on managing a Docker Compose stack, see the How To Use Docker Compose article.
Configure SFTPGo Server
The web administration interface provides initial setup and ongoing configuration management.
Open a web browser and navigate to the SFTPGo admin interface at
https://sftp.example.com/web/admin, replacingsftp.example.comwith your configured domain.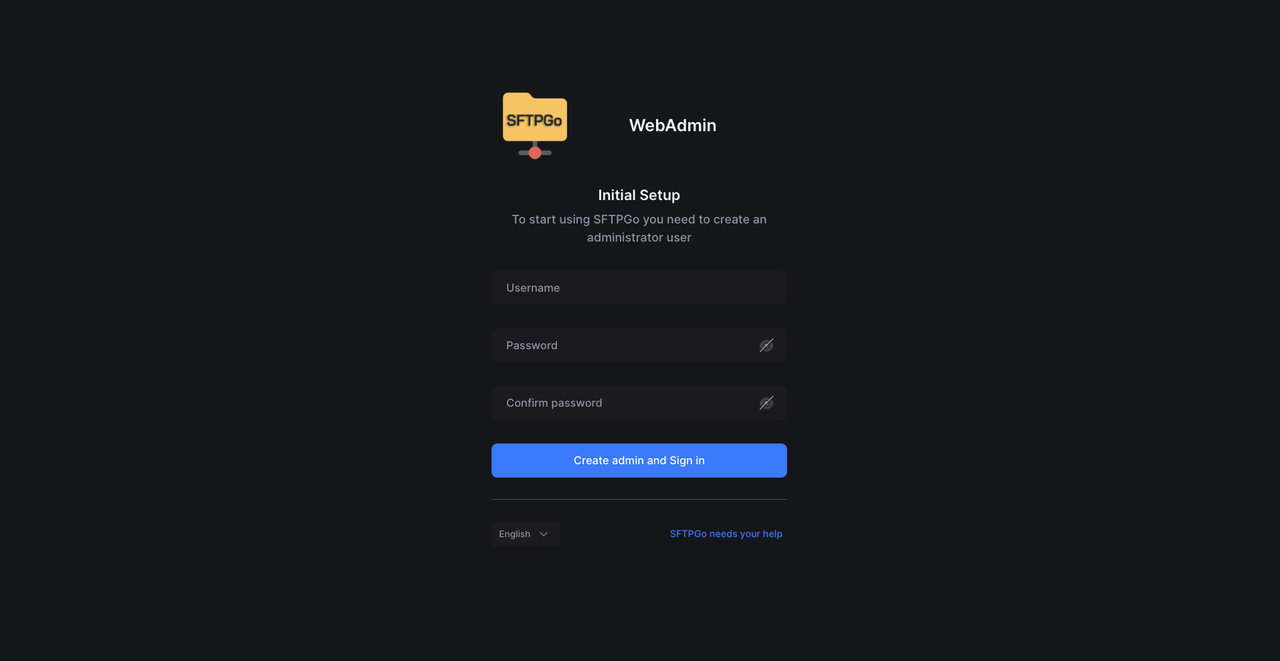
Create the administrator account on first access:
- Enter a username (for example,
admin). - Set a strong password.
- Confirm the password in the Confirm password field.
- Click Create admin and Sign in.
- Enter a username (for example,
After the first login, SFTPGo redirects to the two-factor authentication setup page. Select Default and click Enable.
Scan the QR code with your authenticator app.
Enter the verification code to confirm setup.
Save the recovery codes in a secure location.
Enable SFTPGo Defender
The SFTPGo Defender protects against brute-force login attempts by tracking failed logins and automatically banning offending IP addresses. The Defender is disabled by default and must be enabled through environment variables.
Open the Docker Compose file.
console$ nano ~/sftpgo/docker-compose.yml
Add the following environment variables under the
sftpgoserviceenvironment:block:yaml- SFTPGO_COMMON__DEFENDER__ENABLED=true - SFTPGO_COMMON__DEFENDER__DRIVER=memory - SFTPGO_COMMON__DEFENDER__BAN_TIME=30 - SFTPGO_COMMON__DEFENDER__THRESHOLD=15 - SFTPGO_COMMON__DEFENDER__SCORE_INVALID=2 - SFTPGO_COMMON__DEFENDER__SCORE_VALID=1
Save and close the file.
These variables configure:
DEFENDER__ENABLED: Activates the brute-force protection.DEFENDER__DRIVER: Stores defender events in memory (useproviderfor database-backed persistence).DEFENDER__BAN_TIME: Ban duration in minutes.DEFENDER__THRESHOLD: Score threshold that triggers a ban.DEFENDER__SCORE_INVALID: Score added for invalid login attempts.DEFENDER__SCORE_VALID: Score added for valid logins.
Redeploy the SFTPGo container to apply the changes.
console$ docker compose up -d
Log back in to the admin portal and navigate to IP Manager in the left sidebar. The IP Manager provides two options:
- IP Lists: Manage and add trusted IP addresses to the Defender allow list.
- Auto Block List: View all IP addresses automatically blocked by the Defender.
Set Up User Authentication
SFTPGo supports multiple authentication methods including passwords, SSH public keys, and multi-factor authentication. Create users that mirror your AWS Transfer Family user configuration.
Create an SFTP User with Password Authentication
Password authentication uses a username and password pair stored in the SFTPGo data provider. Each user has an isolated root directory on the local filesystem.
Navigate to Users in the left sidebar.
Click Add to create a new user.
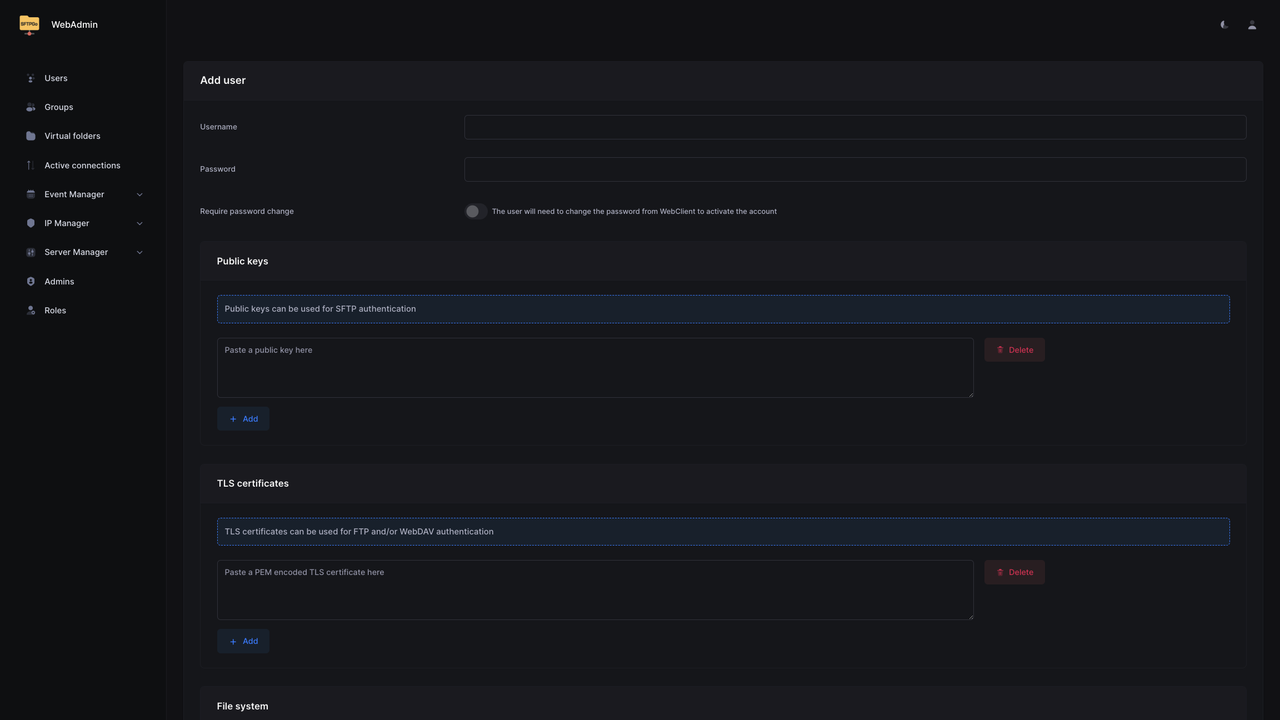
Configure the user account:
- Username: Enter the SFTP username.
- Password: Set a strong password.
- Under Profile, set Status to Active.
Under File system, keep Local disk selected for local storage.
Set the Root directory to
/srv/sftpgo/USERNAME, replacingUSERNAMEwith the SFTP username configured in the previous step.Click Save to create the user.
Configure SSH Key Authentication
SSH key authentication enables passwordless logins using cryptographic key pairs, matching the key-based authentication model used by AWS Transfer Family.
Generate an SSH key pair on the client machine (if not already available).
console$ ssh-keygen -t ed25519 -f ~/.ssh/sftpgo_key -C "sftp-user"
When prompted for a passphrase, press Enter twice to create the key without a passphrase for passwordless authentication.
Display and copy the public key content.
console$ cat ~/.ssh/sftpgo_key.pub
In the SFTPGo web interface, navigate to Users, click Actions next to the target user, and select Edit.
Scroll to the Public keys section.
Paste the entire public key string into the text field.
Click Save.
Test SSH key authentication from the client. Replace
USERNAMEwith the SFTPGo username andsftp.example.comwith your configured domain.console$ sftp -i ~/.ssh/sftpgo_key -P 2022 USERNAME@sftp.example.com
Type
exitto close the SFTP session.consolesftp> exit
Enable Multi-Factor Authentication
Multi-Factor Authentication (MFA) requires users to provide a Time-based One-Time Password (TOTP) code in addition to their primary credentials when accessing protected protocols.
Navigate to Users, click Actions next to the target user, and select Edit.
Expand the ACLs section and locate Require 2FA for.
Select the protocols for which 2FA is required.
Click Save.
The user must configure their authenticator app on next login via the WebClient portal.
Configure Storage Backends
SFTPGo supports multiple storage backends including local filesystem, S3-compatible object storage, Azure Blob, Google Cloud Storage, and SFTP. Each user can have a different backend, allowing you to mix local storage and cloud object storage in the same deployment.
Configure Local Filesystem Storage
Local filesystem is the default storage type for SFTPGo users. Each user requires an explicit root directory path on the host, which maps to a directory inside the mounted /srv/sftpgo volume in the container.
Navigate to Users, click Actions next to the target user, and select Edit.
Under File system, verify Local disk is selected in the Storage dropdown.
Set the Root directory to a path such as
/srv/sftpgo/USERNAMEor any custom path you want. ReplaceUSERNAMEwith the SFTP username.Click Save.
Configure S3-Compatible Object Storage
Connect SFTPGo to any S3-compatible storage service such as MinIO or Vultr Object Storage.
Retrieve your S3-compatible storage credentials from your provider:
- Hostname/Endpoint (for example,
ewr1.vultrobjects.com). - Access Key.
- Secret Key.
- Bucket Name.
- Hostname/Endpoint (for example,
Navigate to Users, click Actions next to the target user, and select Edit.
Under File system, select S3 (Compatible) from the Storage dropdown.
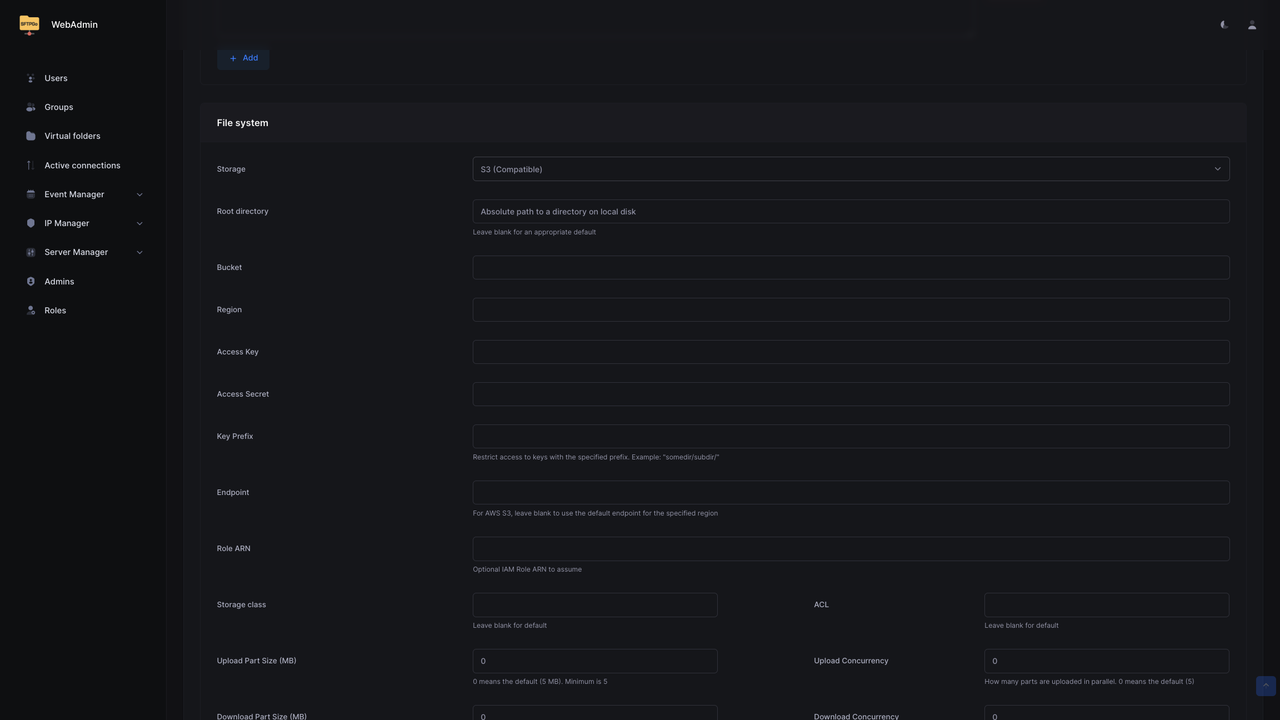
Configure the S3 backend settings:
- Bucket: Enter your bucket name.
- Region: Enter the region code (for example,
ewr1). - Access Key: Enter your access key.
- Access Secret: Enter your secret key.
- Endpoint: Enter the full endpoint URL (for example,
https://ewr1.vultrobjects.com). - Key Prefix: Optionally specify a folder prefix to isolate user data.
Configure the upload settings:
- Enable Use path-style addressing for S3-compatible storage endpoints.
- Set Upload Part Size (MB) to
5(minimum for multipart uploads). - Set Upload Concurrency to
2.
Click Save.
Create a test file on the client machine.
console$ echo "Hello SFTPGo" > testfile.txt
Connect via SFTP to test the configuration. Replace
USERNAMEwith your SFTPGo username andsftp.example.comwith your configured domain.console$ sftp -P 2022 USERNAME@sftp.example.com
Upload the test file.
consolesftp> put testfile.txt
Verify the file appears in the bucket.
consolesftp> lsType
exitto close the SFTP session.consolesftp> exit
S3 Backend Limitations
S3-compatible storage has some limitations compared to local filesystem:
- Resume uploads are disabled by default.
- Symbolic links are not supported.
- Directory rename operations are not atomic.
chmodandchownoperations are silently ignored.
Enable Additional Protocols
SFTPGo runs SFTP on port 2022 by default, but it also supports FTP with TLS (FTP/S) and WebDAV for legacy clients and HTTP-based file access. Enabling these protocols extends SFTPGo to match the protocol coverage of AWS Transfer Family, which supports SFTP, FTP/S, and FTP. Each protocol uses its own listener port and shares the same user accounts, authentication backends, and storage configuration.
FTP with TLS encryption provides compatibility with legacy clients.
Generate or obtain TLS certificates. For testing, create a self-signed certificate. Replace
sftp.example.comwith your configured domain.console$ openssl req -x509 -nodes -days 365 -newkey rsa:2048 \ -keyout ~/sftpgo/config/server.key \ -out ~/sftpgo/config/server.crt \ -subj "/CN=sftp.example.com"
Create the
sftpgo.jsonconfiguration file.console$ nano ~/sftpgo/config/sftpgo.json
Add the following FTP settings:
json{ "ftpd": { "bindings": [ { "port": 2121, "address": "", "tls_mode": 1, "certificate_file": "/var/lib/sftpgo/server.crt", "certificate_key_file": "/var/lib/sftpgo/server.key" } ], "passive_port_range": { "start": 50000, "end": 50100 } } }
Update the Docker Compose file to expose the passive port range.
console$ nano ~/sftpgo/docker-compose.yml
Append the following entry to the existing
ports:block under thesftpgoservice:yaml- "50000-50100:50000-50100"
Save and close the file.
Restart the SFTPGo container to load the new configuration.
console$ docker compose restart sftpgo
Test the FTP/S connection on port
2121using any FTP client such as FileZilla, WinSCP, orlftp.
WebDAV provides HTTP-based file access for web integration.
Open the
sftpgo.jsonconfiguration file.console$ nano ~/sftpgo/config/sftpgo.json
Add the following WebDAV configuration:
json{ "webdavd": { "bindings": [ { "port": 10080, "address": "", "enable_https": false } ] } }
Restart the SFTPGo container to load the new configuration.
console$ docker compose restart sftpgo
Test WebDAV access using
curl. ReplaceUSERNAMEandPASSWORDwith your SFTPGo user credentials andsftp.example.comwith your configured domain.console$ curl -u USERNAME:PASSWORD http://sftp.example.com:10080/
A successful response returns an XML directory listing of the user's WebDAV root.
Set Up Access Controls and Quotas
SFTPGo supports per-user quotas, bandwidth throttling, IP-based restrictions, and directory-level permissions that map directly to AWS Transfer Family's access control features. Each setting applies independently and can be combined to enforce strict resource boundaries.
Configure User Quotas
User quotas restrict how much storage and how many files a user can store.
Navigate to Users, click Actions next to the target user, and select Edit.
Expand the Disk quota and bandwidth limits section and configure:
- Quota size: Maximum storage allowed for the user. Set
0for no limit. The field accepts size suffixes such asMB,GB, orTB. - Quota files: Maximum number of files (for example,
10000).
- Quota size: Maximum storage allowed for the user. Set
Click Save.
Configure Bandwidth Limits
Bandwidth limits cap the maximum upload and download speed for a user.
Navigate to Users, click Actions next to the target user, and select Edit.
Expand the Disk quota and bandwidth limits section and set:
- Bandwidth UL (KB/s): Maximum upload speed (for example,
5120for 5 MB/s). - Bandwidth DL (KB/s): Maximum download speed.
- Bandwidth UL (KB/s): Maximum upload speed (for example,
Click Save.
Configure IP Restrictions
IP restrictions limit which IP addresses or CIDR ranges can connect with a given user account.
Navigate to Users, click Actions next to the target user, and select Edit.
Expand the ACLs section and locate Allowed IP/Mask.
Add allowed IP addresses or CIDR ranges:
text192.168.1.0/24 10.0.0.0/8
Alternatively, configure Denied IP/Mask to block specific addresses.
Click Save.
Configure Directory Permissions
Directory permissions grant fine-grained access controls per path within a user's root directory.
Navigate to Users, click Actions next to the target user, and select Edit.
Expand the ACLs section and under Per-directory permissions, configure directory-level access:
- Click Add to create a new permission entry.
- Specify the Path (for example,
/uploads). - Select allowed operations: List, Download, Upload, Delete, Rename, Create directories.
Click Save.
Configure Event Notifications and Logging
SFTPGo provides built-in logging, syslog forwarding, and HTTP webhook event hooks that replace AWS Transfer Family's CloudWatch integration. Log files capture protocol activity and authentication events, while event hooks trigger actions on filesystem operations such as uploads or downloads.
Configure File Logging
Create the logs directory.
console$ mkdir -p ~/sftpgo/logs
Open the Docker Compose file.
console$ nano ~/sftpgo/docker-compose.yml
Append the logs volume to the existing
volumes:block under thesftpgoservice:yaml- ./logs:/var/log/sftpgo
Append the following logging environment variables to the existing
environment:block under thesftpgoservice:yaml- SFTPGO_LOG_FILE_PATH=/var/log/sftpgo/sftpgo.log - SFTPGO_LOG_MAX_SIZE=10 - SFTPGO_LOG_MAX_BACKUPS=5 - SFTPGO_LOG_MAX_AGE=28 - SFTPGO_LOG_LEVEL=info
Save and close the file.
Redeploy the container.
console$ docker compose up -d
Configure Event Hooks
SFTPGo supports HTTP webhooks for event notifications.
Navigate to Event Manager, then click Actions in the left sidebar.
Click Add to create a new action.
Configure the action:
- Name: Enter an action name (for example,
webhook-action). - Type: Select HTTP.
- Server URL: Enter your webhook URL.
- Method: Select POST.
- Name: Enter an action name (for example,
Click Save.
Click Rules in the left sidebar.
Click Add to create a new event rule.
Configure the event trigger:
- Name: Enter a descriptive name (for example,
upload-notification). - Trigger: Select Filesystem events.
- Filesystem events: Select Upload.
- Name: Enter a descriptive name (for example,
Under Actions, select the action you created in the previous step.
Click Save.
Configure Syslog Integration
Forward logs to a centralized logging system.
Append the following syslog environment variables to the existing
environment:block under thesftpgoservice indocker-compose.yml. ReplaceSYSLOG-SERVERwith your syslog server address.yaml- SFTPGO_SYSLOG__ENABLED=true - SFTPGO_SYSLOG__ADDRESS=udp://SYSLOG-SERVER:514 - SFTPGO_SYSLOG__FACILITY=local0
Redeploy the container.
console$ docker compose up -d
Test the Deployment
Verify the deployment by testing connections across the enabled protocols. The following sections cover password-based SFTP, SSH key-based SFTP, and FTP/S connections.
Test SFTP with Password Authentication
Create a test file on the client machine.
console$ echo "Hello SFTPGo" > testfile.txt
Connect to the SFTP server. Replace
USERNAMEwith your SFTPGo username andsftp.example.comwith your configured domain.console$ sftp -P 2022 USERNAME@sftp.example.com
Enter the password when prompted.
Upload the test file.
consolesftp> put testfile.txt
Download the file to verify.
consolesftp> get testfile.txt /tmp/testfile-downloaded.txt
List the directory contents.
consolesftp> ls -la
Exit the session.
consolesftp> exit
Test SFTP with SSH Key Authentication
Connect using the private key. Replace
USERNAMEwith your SFTPGo username andsftp.example.comwith your configured domain.console$ sftp -i ~/.ssh/sftpgo_key -P 2022 USERNAME@sftp.example.com
The SFTP session opens without prompting for a password, confirming SSH key authentication is working.
Type
exitto close the session.consolesftp> exit
Test FTP/S with lftp
Install the
lftpclient on the local machine.console$ sudo apt install lftp -y
Connect with explicit TLS. Replace
USERNAMEwith your FTP username andsftp.example.comwith your configured domain.console$ lftp -u USERNAME -p 2121 ftp://sftp.example.com
List files to verify the connection.
consolelftp> lsType
exitto close the session.consolelftp> exit
Migrate from AWS Transfer Family to SFTPGo
Migrating from AWS Transfer Family to SFTPGo involves exporting users, transferring file data, and updating client connection details. The following subsections cover each migration phase along with AWS-specific features that require manual reconfiguration.
User Migration
Export user configurations from AWS Transfer Family and recreate them in SFTPGo.
List AWS Transfer Family users using the AWS CLI.
console$ aws transfer list-users --server-id SERVER-ID
Export user details including SSH keys.
console$ aws transfer describe-user --server-id SERVER-ID --user-name USERNAME
For each user, note the following information:
- Username.
- SSH public keys.
- Home directory mapping.
- IAM role (for permission reference only — IAM roles cannot be directly migrated to SFTPGo).
Generate an SFTPGo API access token using the admin credentials. Replace
ADMIN-USERNAMEandADMIN-PASSWORDwith your SFTPGo admin credentials andsftp.example.comwith your configured domain.console$ curl -u ADMIN-USERNAME:ADMIN-PASSWORD https://sftp.example.com/api/v2/token
The response contains an
access_tokenvalue. The token expires after 15 minutes. Copy it and complete the next step before it expires.Create corresponding users in SFTPGo via the REST API.
console$ curl -X POST "https://sftp.example.com/api/v2/users" \ -H "Authorization: Bearer ACCESS-TOKEN" \ -H "Content-Type: application/json" \ -d '{ "username": "USERNAME", "password": "PASSWORD", "status": 1, "public_keys": ["SSH-PUBLIC-KEY"], "home_dir": "/srv/sftpgo/data/USERNAME", "permissions": {"/": ["*"]} }'
Replace:
sftp.example.comwith your configured domain.ACCESS-TOKENwith the token from the previous step.USERNAMEwith the new SFTP username.PASSWORDwith a strong password for the user.SSH-PUBLIC-KEYwith the user's SSH public key string.
The
"status": 1field activates the user account. Without it, the user is created in a disabled state and cannot log in.
Data Migration
Transfer files from S3 to your SFTPGo storage backend.
If using S3 backend with SFTPGo, configure the same bucket or migrate data between buckets:
console$ aws s3 sync s3://transfer-family-bucket s3://sftpgo-bucket
For local filesystem backend, use the AWS CLI to download files:
console$ aws s3 sync s3://transfer-family-bucket ~/sftpgo/data/USERNAME/
Set correct ownership on downloaded files.
console$ sudo chown -R 1000:1000 ~/sftpgo/data/
Authentication Migration
Convert AWS IAM-based authentication to SFTPGo methods.
| AWS Authentication | SFTPGo Equivalent |
|---|---|
| SSH Public Keys | Public Keys (direct migration). |
| IAM User Credentials | Password Authentication. |
| AWS Directory Service | LDAP Plugin. |
| Custom Identity Provider | External Authentication Hook. |
For custom identity providers, configure an external authentication hook:
Create an authentication script or HTTP endpoint that validates credentials.
Configure SFTPGo to use external authentication:
json{ "data_provider": { "external_auth_hook": "http://auth-server:8000/validate", "external_auth_scope": 0 } }
Client Configuration Updates
Update client applications with the new endpoint information.
Document the new connection parameters:
- Host:
sftp.example.com(your SFTPGo server). - Port:
2022(SFTP). - Authentication: SSH key or password.
- Protocol: SFTP.
- Host:
Distribute updated connection profiles to users.
Update automated scripts and integrations with the new endpoint.
Test each client configuration before decommissioning AWS Transfer Family.
Things to Consider During Migration
Address the following AWS-specific features when migrating:
- IAM Role Permissions: Map IAM policy permissions to SFTPGo user permissions. SFTPGo uses directory-level permissions rather than IAM policies.
- S3 Lifecycle Policies: SFTPGo does not manage S3 lifecycle rules. Configure lifecycle policies directly in your S3-compatible storage provider.
- CloudWatch Logs: Replace CloudWatch logging with SFTPGo's built-in logging, syslog forwarding, or webhook integrations.
- VPC Endpoints: AWS Transfer Family VPC endpoints provide private connectivity. For SFTPGo, use private networks or VPN connections for internal-only access.
- Managed Host Keys: AWS Transfer Family manages SSH host keys automatically. Export the host key from SFTPGo (
/var/lib/sftpgo/id_*) and distribute the fingerprint to clients to prevent man-in-the-middle warnings. - Elastic IPs: If clients rely on static IP addresses, configure a reserved IP on your server.
Conclusion
You have successfully deployed SFTPGo as a self-hosted alternative to AWS Transfer Family using Docker Compose with Traefik for automatic HTTPS. The configuration includes multi-protocol support (SFTP, FTP/S, WebDAV), S3-compatible storage backends, user authentication with SSH keys and passwords, user quotas, bandwidth throttling, IP restrictions, and per-directory permissions. For advanced configuration options including clustering, plugins, and enterprise features, visit the official SFTPGo documentation.