How to Deploy Hermes Agent – Open-Source Self-Hosted AI Agent
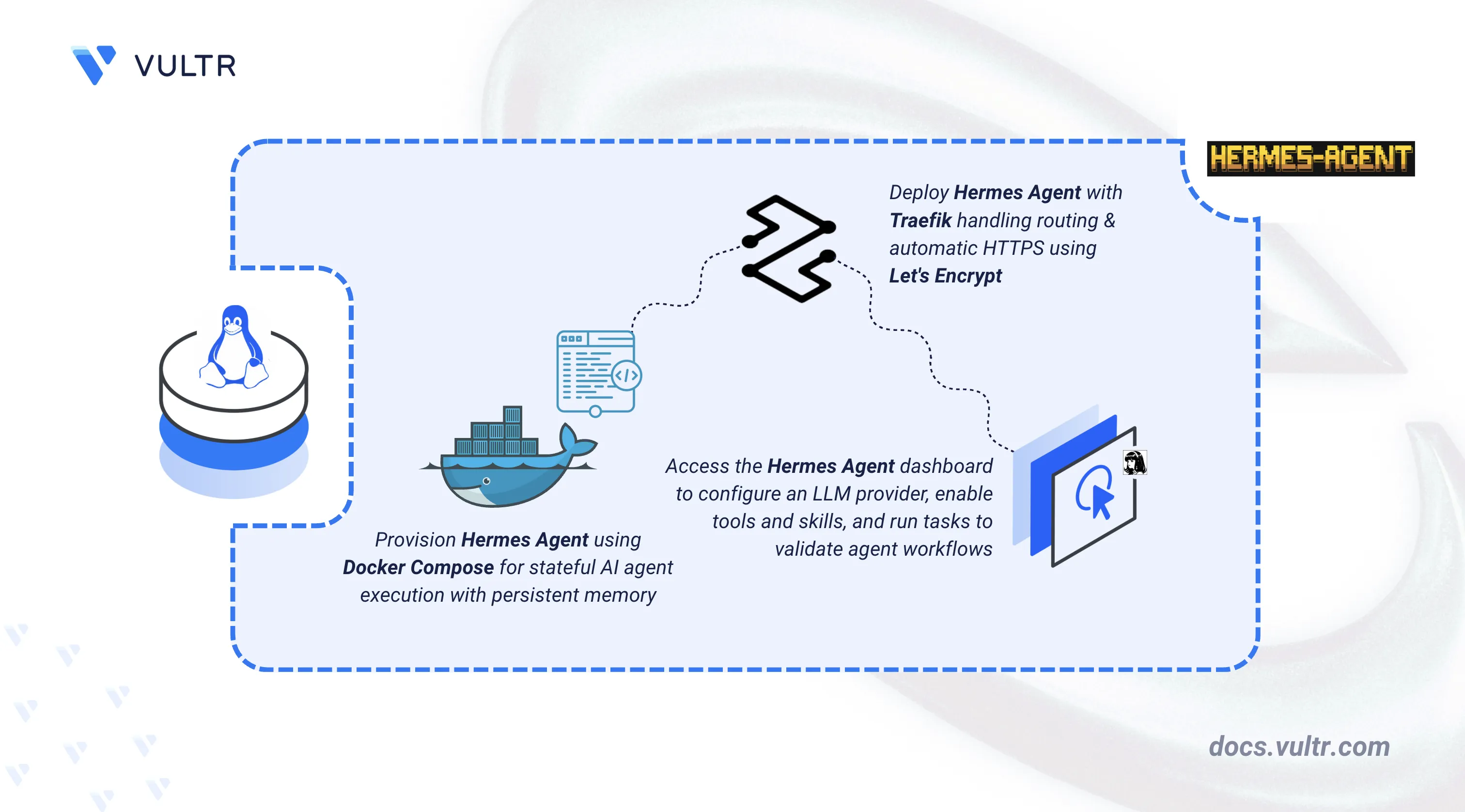
Hermes Agent is an open-source, self-hosted AI agent developed by Nous Research. It features persistent memory, autonomous skill creation, and multi-platform messaging integrations including Telegram, Discord, Slack, and WhatsApp. Unlike chatbot wrappers or IDE-bound copilots, Hermes Agent runs continuously on your server, learns from interactions, and improves its capabilities over time.
This article explains how to deploy Hermes Agent on a Linux server using Docker Compose with Traefik for automatic HTTPS. It covers directory setup, environment configuration, LLM provider setup (including free access via Nous Portal and optional integration with Vultr Serverless Inference), and demonstrates the application by creating a task and verifying persistent memory.
Prerequisites
Before you begin, you need to:
- Have access to a Linux-based server as a non-root user with sudo privileges.
- Install Docker and Docker Compose.
- Create a DNS A record pointing to your server's IP address (for example,
hermes.example.com). - (Optional) Have an API key for a model provider such as OpenAI, Anthropic, or OpenRouter. You can use Nous Portal for free access via OAuth, or configure Vultr Serverless Inference as shown later in this article.
Set Up the Directory Structure, Configuration, and Environment Variables
Hermes Agent stores all user data including configuration, API keys, sessions, skills, and memories in a persistent data directory. The Docker container mounts this directory to preserve state across restarts and upgrades.
Create the project directory with subdirectories for persistent data.
console$ mkdir -p ~/hermes/data
data/: Persists Hermes Agent configuration, sessions, skills, and memory files.
Navigate to the project directory.
console$ cd ~/hermes
Create the environment file.
console$ nano .env
Add the following configuration. Replace
hermes.example.comwith your domain name andadmin@example.comwith your email address.iniDOMAIN=hermes.example.com LETSENCRYPT_EMAIL=admin@example.com
Save and close the file.
Deploy with Docker Compose
Docker Compose orchestrates the Hermes Agent gateway, dashboard, and Traefik reverse proxy. The gateway handles messaging integrations and agent execution, while the dashboard provides a web interface for monitoring and configuration. This setup extends the official Docker deployment guide with Traefik for automatic HTTPS and basic authentication.
Generate a hashed password file for Traefik basic authentication. Replace
DASHBOARD_USERNAMEwith your preferred username andSTRONG_DASHBOARD_PASSWORDwith a secure password.console$ docker run --rm httpd:2.4-alpine htpasswd -nbB DASHBOARD_USERNAME 'STRONG_DASHBOARD_PASSWORD' > .htpasswd
Create the Docker Compose file.
console$ nano docker-compose.yml
Add the following configuration.
yamlservices: traefik: image: traefik:v3.6.15 container_name: traefik command: - "--providers.docker=true" - "--providers.docker.exposedbydefault=false" - "--entrypoints.web.address=:80" - "--entrypoints.websecure.address=:443" - "--entrypoints.web.http.redirections.entrypoint.to=websecure" - "--entrypoints.web.http.redirections.entrypoint.scheme=https" - "--certificatesresolvers.letsencrypt.acme.httpchallenge=true" - "--certificatesresolvers.letsencrypt.acme.httpchallenge.entrypoint=web" - "--certificatesresolvers.letsencrypt.acme.email=${LETSENCRYPT_EMAIL}" - "--certificatesresolvers.letsencrypt.acme.storage=/letsencrypt/acme.json" ports: - "80:80" - "443:443" volumes: - "/var/run/docker.sock:/var/run/docker.sock:ro" - "letsencrypt:/letsencrypt" - "./.htpasswd:/etc/traefik/.htpasswd:ro" restart: unless-stopped hermes: image: nousresearch/hermes-agent:v2026.4.30 container_name: hermes command: gateway run volumes: - ./data:/opt/data expose: - "8642" restart: unless-stopped dashboard: image: nousresearch/hermes-agent:v2026.4.30 container_name: hermes-dashboard command: dashboard --host 0.0.0.0 --port 9119 --no-open --insecure environment: - GATEWAY_HEALTH_URL=http://hermes:8642 volumes: - ./data:/opt/data depends_on: - hermes deploy: resources: limits: memory: 512M cpus: "0.5" labels: - "traefik.enable=true" - "traefik.http.routers.hermes.rule=Host(`${DOMAIN}`)" - "traefik.http.routers.hermes.entrypoints=websecure" - "traefik.http.routers.hermes.tls.certresolver=letsencrypt" - "traefik.http.services.hermes.loadbalancer.server.port=9119" - "traefik.http.middlewares.hermes-auth.basicauth.usersfile=/etc/traefik/.htpasswd" - "traefik.http.routers.hermes.middlewares=hermes-auth" restart: unless-stopped volumes: letsencrypt:
Save and close the file.
In the above manifest:
- traefik: Serves as the reverse proxy and TLS termination point with automatic Let's Encrypt certificate provisioning. Mounts the
.htpasswdfile for basic authentication. - hermes: Runs the Hermes Agent gateway that handles messaging integrations and agent execution.
- dashboard: Provides a web interface for monitoring agent activity, viewing sessions, and managing configuration. The
--insecureflag allows binding to0.0.0.0, which is safe because Traefik handles HTTPS. Thebasicauth.usersfilelabel configures basic authentication for dashboard access. - volumes: The
./datamount persists all Hermes Agent state including OAuth tokens from Nous Portal. Theletsencryptvolume stores TLS certificates.
- traefik: Serves as the reverse proxy and TLS termination point with automatic Let's Encrypt certificate provisioning. Mounts the
Build and start all services in detached mode.
console$ docker compose up -d
Verify all services are running.
console$ docker compose ps -a
Output:
NAME IMAGE COMMAND SERVICE CREATED STATUS PORTS hermes nousresearch/hermes-agent:v2026.4.30 "/usr/bin/tini -g --…" hermes 9 seconds ago Up 8 seconds 8642/tcp hermes-dashboard nousresearch/hermes-agent:v2026.4.30 "/usr/bin/tini -g --…" dashboard 8 seconds ago Up 8 seconds traefik traefik:v3.6.15 "/entrypoint.sh --pr…" traefik 9 seconds ago Up 8 seconds 0.0.0.0:80->80/tcp, [::]:80->80/tcp, 0.0.0.0:443->443/tcp, [::]:443->443/tcpView the logs for the services.
console$ docker compose logs
For more information on managing a Docker Compose stack, see the How To Use Docker Compose article.
Access and Configure Hermes Agent
After deployment, configure your LLM provider and access the dashboard.
Configure your LLM provider using the
hermes modelcommand.console$ docker run -it --rm \ -v ~/hermes/data:/opt/data \ nousresearch/hermes-agent:v2026.4.30 model
Select your preferred provider. For free access, choose Nous Portal and complete the OAuth authentication flow. You can also select OpenAI, Anthropic, OpenRouter, or other providers and enter API keys when prompted. For Vultr Serverless Inference, see the optional configuration section later in this article. The configuration is saved to the data directory and persists across container restarts.
Open a web browser and navigate to
https://hermes.example.com. Replacehermes.example.comwith your configured domain.Enter the basic authentication credentials when prompted (the
DASHBOARD_USERNAMEandSTRONG_DASHBOARD_PASSWORDyou used when generating the.htpasswdfile).Verify the dashboard displays the agent status and active sessions.
Navigate to the Config section in the dashboard to review model settings, memory preferences, and messaging integrations.
Verify the Hermes Agent Application
Testing core agent functionality confirms that memory persistence, skill execution, and the LLM integration work correctly.
Open a terminal session with the agent.
console$ docker run -it --rm \ -v ~/hermes/data:/opt/data \ nousresearch/hermes-agent:v2026.4.30
This opens an interactive chat session with the Hermes Agent.
Send a test message to verify the LLM connection.
What is your name and what can you do?The agent responds with its capabilities and confirms the configured LLM provider (Nous Portal, OpenAI, Anthropic, or OpenRouter) is working.
Test persistent memory by asking the agent to remember information.
Remember that my favorite programming language is Python.Exit the chat session by typing
/exitorCtrl+C, then start a new session.console$ docker run -it --rm \ -v ~/hermes/data:/opt/data \ nousresearch/hermes-agent:v2026.4.30
Verify memory persistence by asking about the stored information.
What is my favorite programming language?The agent recalls the previously stored information, confirming persistent memory is working.
Test a built-in tool by asking the agent to perform a task.
What is the current date and time?The agent uses its tools to retrieve and display the current timestamp.
Use Vultr Serverless Inference (Optional)
Hermes Agent supports custom model providers through OpenAI-compatible endpoints. Configure Vultr Serverless Inference as a model provider to access additional AI models.
Enable Vultr Serverless Inference in the Vultr Console and copy your API key.
Add your Vultr API key to the environment file. Replace
YOUR-VULTR-API-KEYwith your Vultr API key.console$ nano ~/hermes/.env
Add the following line:
iniVULTR_API_KEY=YOUR-VULTR-API-KEY
Save and close the file.
Edit the Hermes configuration file.
console$ sudo nano ~/hermes/data/config.yaml
Find the
providers: {}line and replace it with the Vultr configuration:yamlproviders: vultr: base_url: https://api.vultrinference.com/v1 key_env: VULTR_API_KEY
Save and close the file.
Restart the Hermes services to apply the new configuration.
console$ docker compose restart hermes dashboard
Start an interactive chat session. Pass the environment file so the Vultr provider is available in the model picker.
console$ docker run -it --rm \ -v ~/hermes/data:/opt/data \ --env-file ~/hermes/.env \ nousresearch/hermes-agent:v2026.4.30
Switch to a Vultr model using the model picker. Type
/modelto open the interactive picker./modelSelect vultr from the provider list, then choose a model such as
moonshotai/Kimi-K2.6ordeepseek-ai/DeepSeek-V4-Pro.Verify the model responds correctly by sending a test message.
What model is currently being used?Output:
The current model is moonshotai/Kimi-K2.6 (served via Vultr).The agent responds with its model name and confirms it is served via Vultr, indicating the integration works correctly.
Conclusion
You have deployed Hermes Agent on a Linux server using Docker Compose with Traefik for automatic HTTPS and basic authentication for dashboard access. The setup provides a self-hosted AI agent with persistent memory, autonomous skill creation, and support for multiple LLM providers including Nous Portal (free MiMo v2 Pro access), OpenAI, Anthropic, OpenRouter, and Vultr Serverless Inference. For messaging platform integrations, scheduled automations, and advanced configuration, refer to the official Hermes Agent documentation.